October 2, 2025

A variety of malicious payloads delivered through similar fake invitations
Example usage:
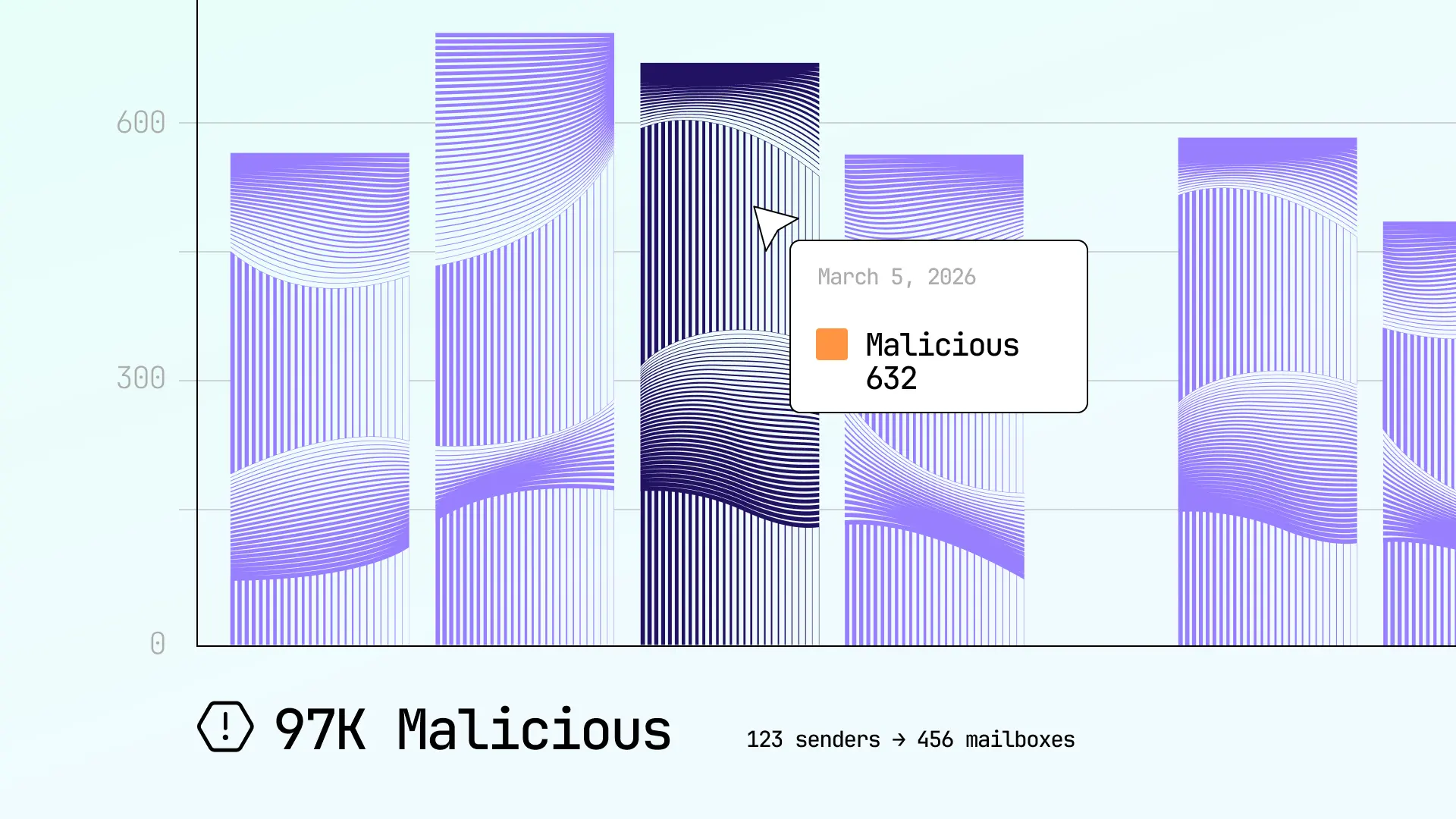
Enhanced reporting and analytics provide complete visibility into email security gcocrdsetup
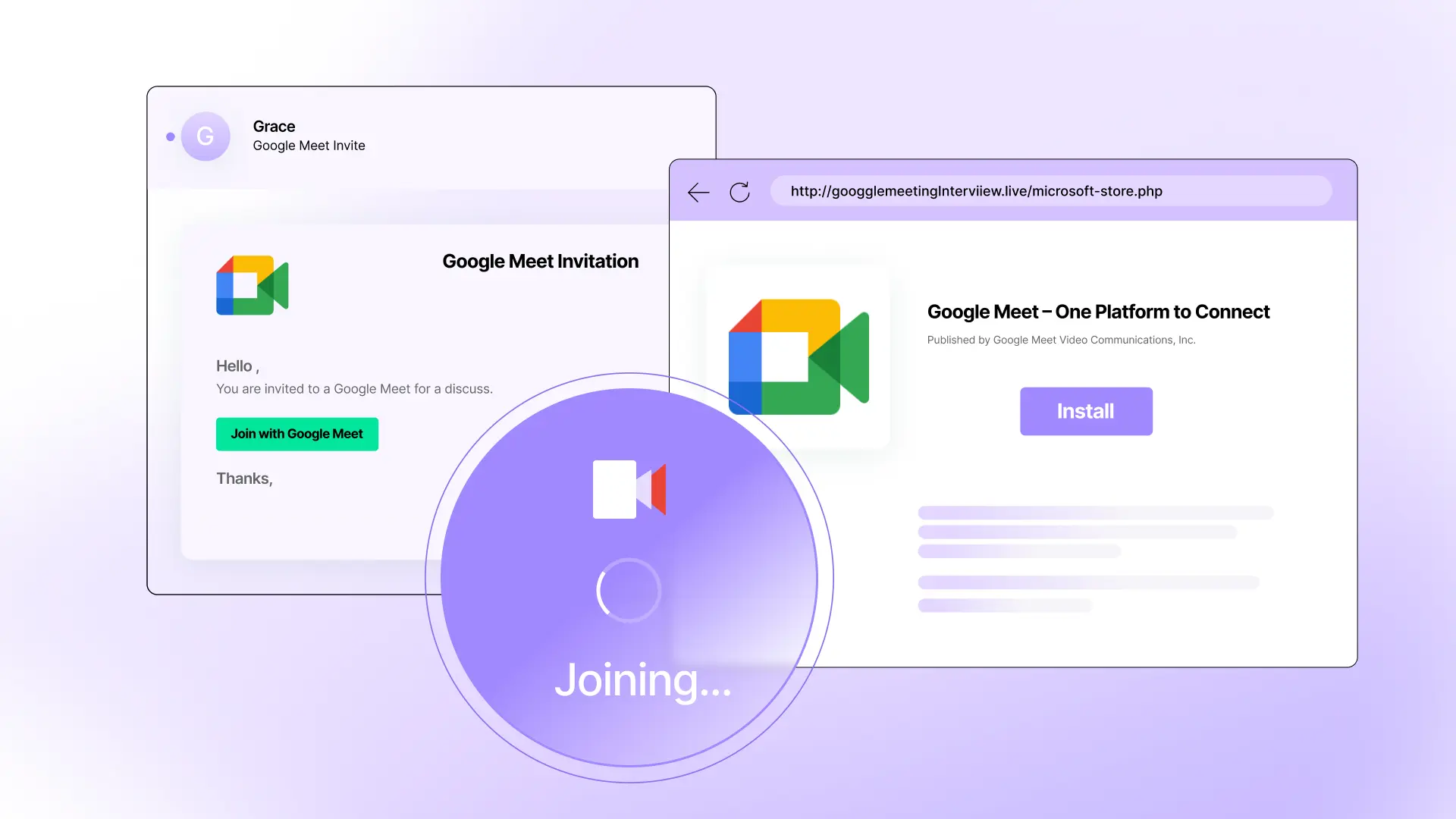
Fake Google Meet invitation, fake Microsoft Store, real malware attack Example usage:


See how Sublime delivers autonomous protection by default, with control on demand.
.svg)